[ SECURITY ]
· 7 min read
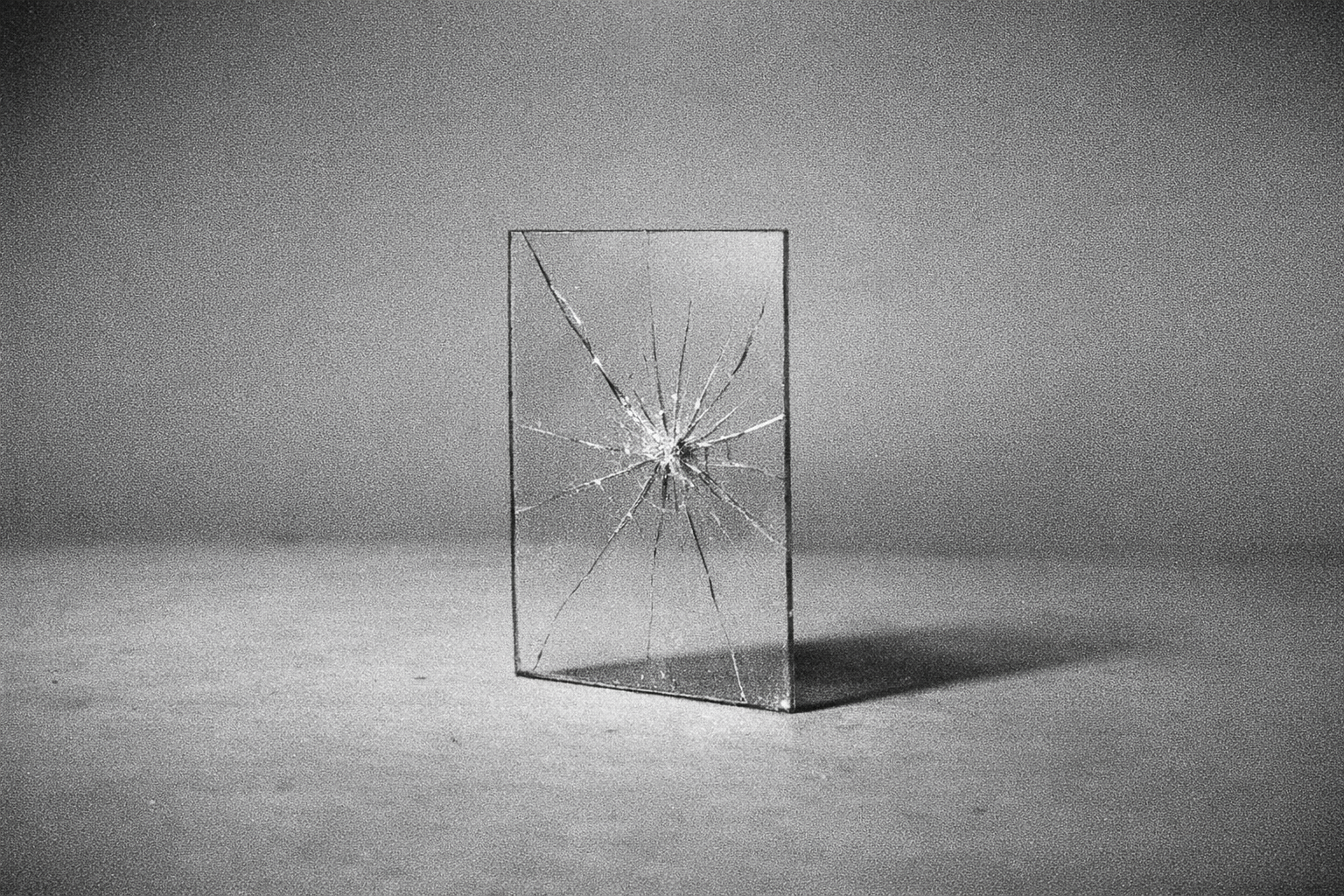
Trust is a vulnerability
In cybersecurity, trust is an attack surface. Every AI privacy promise depends on trusting the company, every employee, every future acquirer, and every government that might compel disclosure.
Trust as attack surface
In cybersecurity, every point of trust is a potential point of failure. When you trust a company with your data, you are not making a single decision. You are trusting every employee who has database access, every contractor who touches the infrastructure, every third-party vendor in the supply chain, every future executive who might change the company's direction, and every government that might compel disclosure. Each of these represents an attack surface. The more entities you trust, the larger your exposure. Security professionals understand this instinctively, which is why zero-trust architecture has become the standard for protecting critical systems. The principle is simple: do not grant trust that you cannot verify, and minimize the number of entities that require trust in the first place.
The track record of broken promises
The history of tech company privacy promises is a history of broken commitments. Google adopted "Don't be evil" as its motto, then built the largest surveillance advertising network in history. Facebook promised users control over their data, then enabled Cambridge Analytica to harvest millions of profiles for political targeting. Anthropic marketed itself as the safety-focused alternative to OpenAI, then updated its privacy policy to allow training on user conversations by default with a five-year retention window. Each company made sincere-sounding commitments that were abandoned when business incentives changed. The pattern is not a matter of individual corporate malice. It is the predictable result of trusting organizations whose obligations to shareholders will always outweigh their commitments to users when the two come into conflict.
The insider threat
Even companies with genuine privacy commitments cannot eliminate the insider threat. Every employee with database access is a potential point of compromise. Disgruntled workers, social engineering targets, bribery candidates, and simple human error all create pathways to data exposure. Major breaches at companies with sophisticated security programs demonstrate that no organization can fully secure data against internal threats. The more sensitive the data, the higher the value of compromise, and the more motivated the potential attackers. AI conversation data is among the most sensitive information any company holds. It contains health concerns, financial details, relationship problems, and professional vulnerabilities. The value of this data to malicious insiders is proportional to its intimacy.
Government compulsion and legal demands
Companies that hold user data are subject to legal demands from governments worldwide. Subpoenas, national security letters, court orders, and regulatory requirements can compel disclosure regardless of the company's privacy policy. In many jurisdictions, companies are prohibited from even informing users that their data has been accessed. The legal frameworks for compelling data disclosure are expanding, not contracting. Governments have recognized that AI conversation data is a valuable intelligence source and are building the legal mechanisms to access it. A company can promise not to share your data voluntarily, but it cannot promise to resist a court order. The only way to ensure your data is not disclosed under legal compulsion is to ensure the company does not have it in the first place.
Why policy-based privacy always fails
Privacy policies are promises written in language designed to be changed. They include clauses allowing unilateral modification with minimal notice. They define terms broadly enough to permit practices that users would not expect. They create the appearance of protection while preserving maximum flexibility for the company. Policy-based privacy fails because it depends on the continued alignment of the company's interests with the user's interests. That alignment is temporary. When a company faces financial pressure, competitive threats, regulatory demands, or acquisition offers, user privacy is the first commitment to be renegotiated. The only privacy that survives these pressures is privacy that does not depend on anyone's continued good behavior. Architectural privacy, enforced by encryption and system design rather than policy documents, is the only kind that endures.
SecureGPT's zero-trust architecture
SecureGPT is designed so that you do not need to trust anyone, including SecureGPT. Your messages are encrypted with RSA-2048 on your device before transmission. The server, running on trusted, eco-friendly servers located in Canada and the EU, decrypts, processes, and discards. There is no conversation database to subpoena, no user profiles for insiders to access, no data retention for governments to compel disclosure of. The system is stateless. SecureGPT runs on open-source models like Mistral and LLaMA, so the code and the models are inspectable. Privacy is not a policy that can be revised. It is an architectural property enforced by encryption. Trust is a vulnerability, and SecureGPT is built to eliminate it.